How to know if a SharePoint tenant blocks apps not using modern authentication
TL;DR - Send an anonymous OPTIONS call to your SharePoint Online tenant domain and read the response + headers.
Out of the box, SharePoint Online allows someone to authenticate through either the older claims-based authentication, or the newer modern authentication.
Claims uses Microsoft Online as a Security Token Service and will provide a token with all the user’s access rights; Modern uses the Active Directory Authentication Libraries (ADAL) and OAuth 2.0, and provides a much more granular permission mechanism and it is recommended that people authenticate using Modern where possible.
The SharePoint admin center has an option to block access to any third-party application that doesn’t use modern authentication. This includes Outlook 2010 so depending on your organization it is not always possible to do this blocking. You can find this in Policies > Access Control.
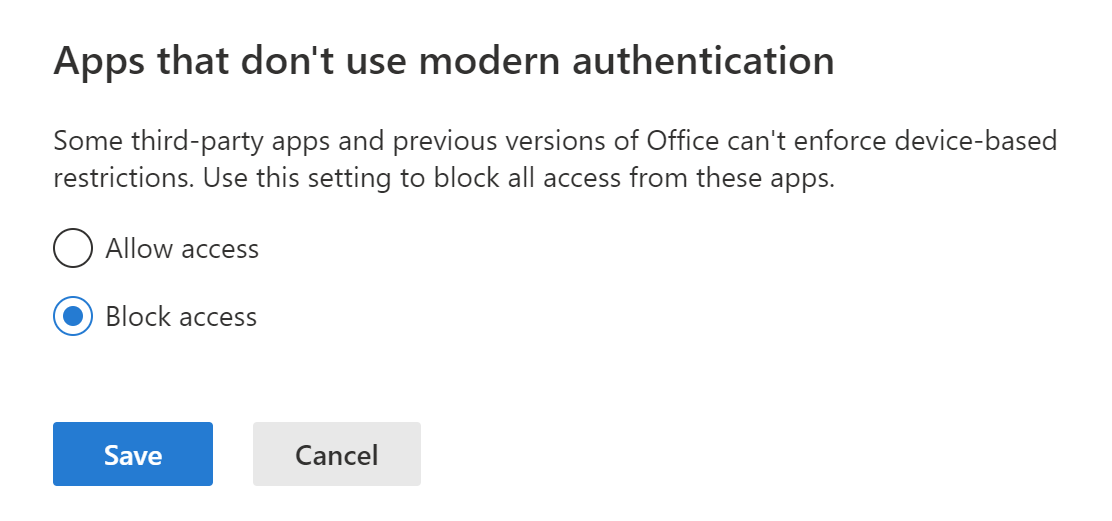
Block access to apps that don’t use modern authentication
Recently I came across an issue where an application I was working on needed to know if the SharePoint Online tenant has blocked apps that don’t use modern authentication. This proved quite challenge until I found an article on how SharePoint Designer works with modern authentication.
After a bit of fiddling, all it needs is an anonymous OPTIONS call to the SharePoint online domain and to read the response headers.
OPTIONS https://yourtenant.sharepoint.com
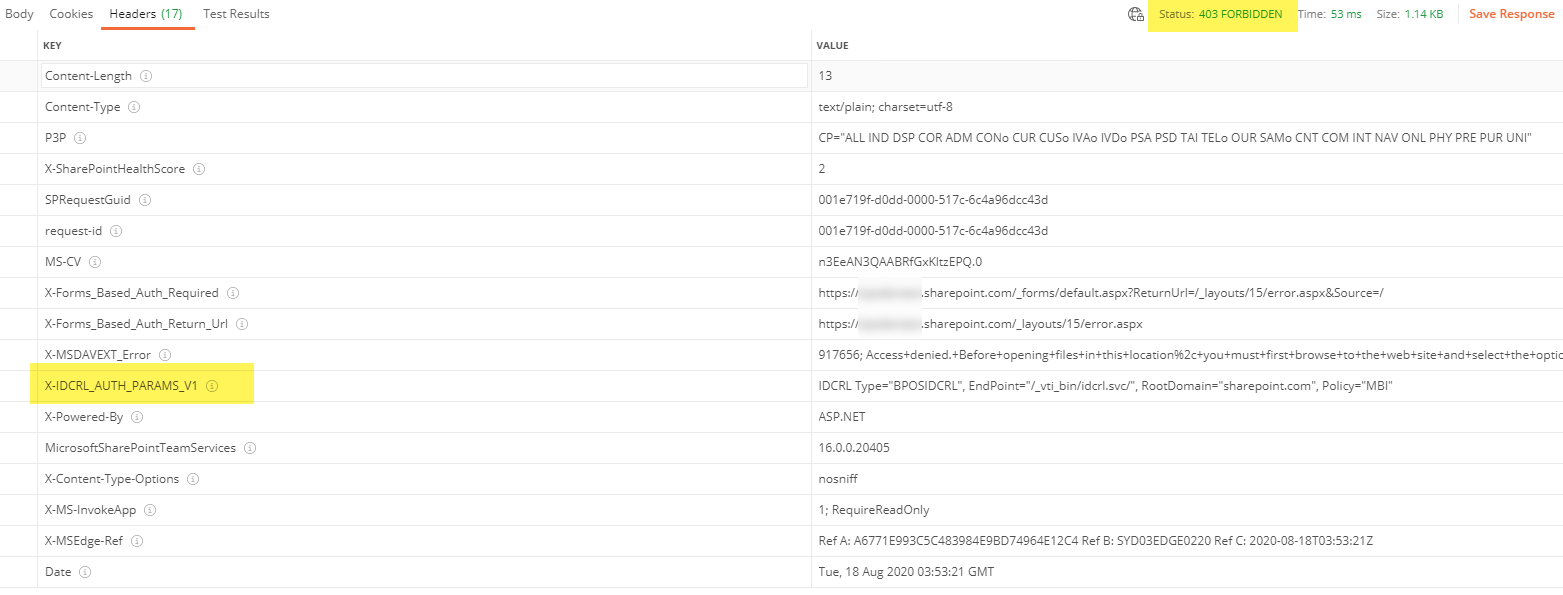
When claims authentication is enabled, a 403 response is returned with a header named X-IDCRL_AUTH_PARAMS_V1; this refers to the Identity Client Runtime Library, and from what I can understand talks to the claims provider for SharePoint Online.
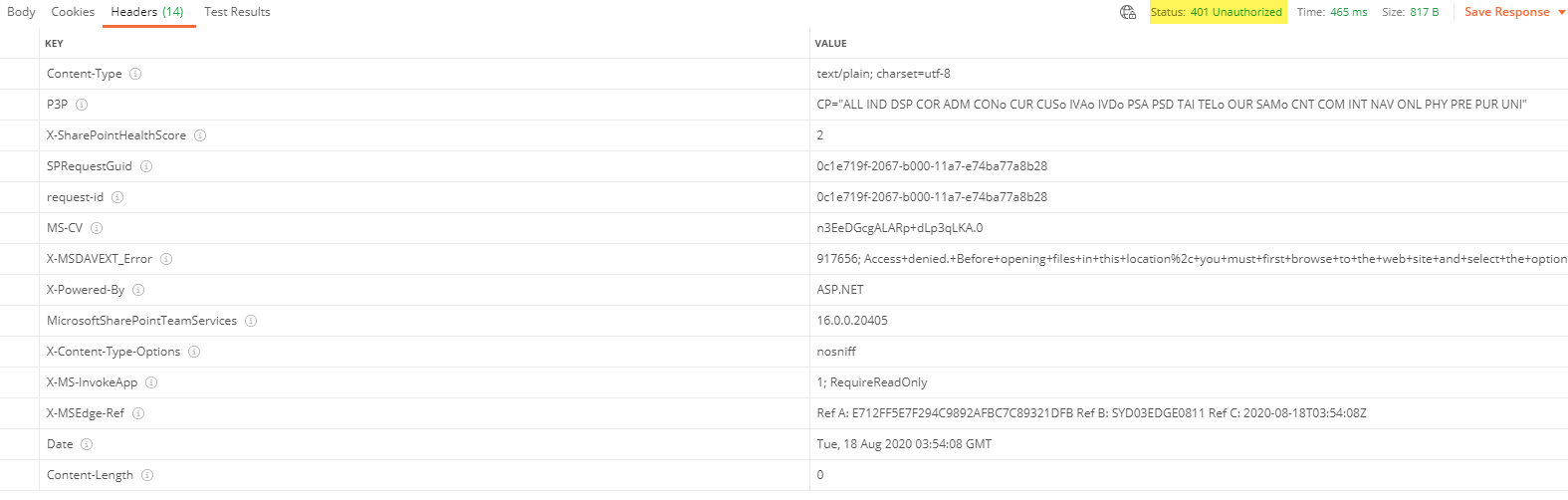
When claims authentication is blocked, a 401 is returned without the X-IDCRL_AUTH_PARAMS_V1 header. No claims, no header.
This has been confirmed with a few tenants with separate settings, and seems to hold true.